Microsoft has fixed a new Windows RPC CVE-2022-26809 vulnerability that raises concerns among security researchers because of its potential for widespread, significant cyber attacks once an exploit is developed. Therefore, all organizations should apply Windows security updates as soon as possible.
Microsoft resolved this vulnerability as part of the April 2022 Patch Tuesday updates and rated it as ‘Critical’ as it allows unauthorized remote code execution via a bug in the Microsoft Remote Procedure Call (RPC) communication protocol.
If utilized, all commands will be executed at the same privilege level as the RPC server, which in many cases has elevated permissions or SYSTEM level, giving full administrative access to the utilized device.
The Microsoft Remote Procedure Call (RPC) protocol is a communication protocol that allows processes to communicate with each other even when these programs are running on a different device.
RPC allows processes on different devices to communicate with each other, with RPC hosts listening for remote connections over TCP ports, most often ports 445 and 135.
CVE-2022-26809 in the reticle
After Microsoft released security updates, security researchers quickly saw the potential for this flaw to be exploited in widespread attacks, similar to what we saw with the 2003 Blaster worm and the 2017 Wannacry attacks that exploited the Eternal Blue vulnerability.
Researchers have already begun to analyze and publish technical details about the vulnerability that other researchers and threat actors will use to piece together for a usable exploitation.
For example, researchers at Akamai have already tracked the error down to a heap buffer overflow in the rpcrt4.dll DLL.
“As we dived deeper into the vulnerable code in OSF_SCALL: GetCoalescedBuffer, we noticed that the integer overflow error could lead to a heap buffer overflow where data is copied to a buffer that is too small to populate,” Akamai explained in their technical overview.
“This in turn makes it possible to write data out of the buffer boundaries on the heap. When used properly, this primitive can lead to remote code execution.”
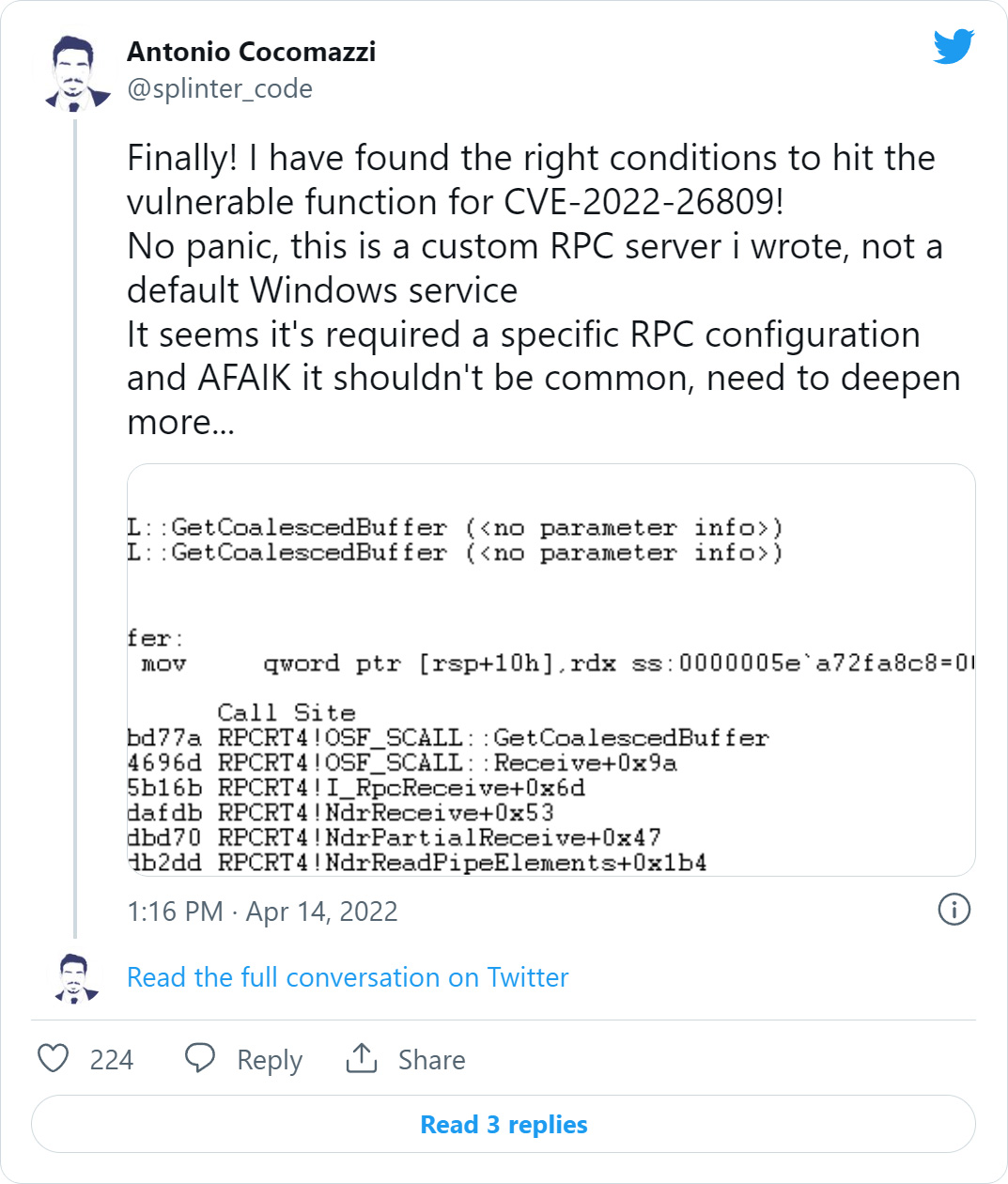
Sentinel One researcher Antonio Cocomazzi has also played with the bug and successfully exploited it on a custom RPC server, not a built-in Windows service.
The good news is that it may require a specific RPC configuration to be vulnerable, but it is still being analyzed.
While researchers are still working to find out the full technical details of the error and how to reliably exploit it, says security researcher Matthew Hickeyco-founder of Hacker House, has also played with analyzing the vulnerability.
Hickey told BleepingComputer that it is only a matter of time before an exploit is developed and that it may have the potential for harmful results.
“It’s as bad as it can get for Windows enterprise systems, it’s important to emphasize that people should use the patch because it can show up in a variety of configurations of both client and server RPC services,” said Hickey to BleepingComputer in a conversation about insect.
“This has the potential to become yet another global event similar to WCRY, depending on how long it takes attackers to arm and exploit. I would expect attacks to start increasing with this vulnerability in the coming weeks.”
Hickey tells BleepingComputer that the vulnerable DLL, rpcrt4.dll, is not only used by Microsoft services but also by other applications, further increasing the vulnerability of this vulnerability.
“The main problem is that because it’s in rpcrt4.dll, not only standard Microsoft services, but all sorts of third-party programs will be affected, so even if you just block the regular Windows ports, you may still have some software, it is both vulnerable in client / server mode – things like backup agents, antivirus, endpoint software, even the latest tools that use RPC. “
Will Dormann, Vulnerability Analyst at CERT / CC, warns that all administrators should block port 445 at the network perimeter so that vulnerable servers are not exposed to the Internet. By blocking port 445, the devices are not only protected from external threat actors, but also from potential network worms that could exploit the exploit.
Unless security updates are installed, however, devices will still be vulnerable internally to threat actors compromising a network.
Since this vulnerability is ideal for spreading laterally within a network, we’ll almost certainly see it being used by ransomware gangs in the future.
While it is not time to panic about this vulnerability, administrators should make patching these devices a priority, as exploitation can be released at any time.
Once a exploit is released, it usually only takes a short time for threatening actors to arm it in attack.